Get Ahead of New SEC Cybersecurity Rules and Save 20%. Learn More

Simplify vendor security assessments intuitively and with flexibility
Vendor security is a critical component of meeting regulatory requirements and building a complete cybersecurity strategy.
Vendor Risk Management is changing how companies assess vendor security risk
Working with vendors is crucial to your organization's compliance and risk needs. It's vital that the vendors you partner with can be trusted to access, handle and transmit your company's most sensitive information. Smarsh Vendor Risk Management provides effective third-party risk management to keep organizations in regulatory compliance and mitigate risk without the headache – automating and simplifying the most resource-intensive parts of third-party risk evaluation and management.
Key Benefits
Vendor Risk Management does the hard work for you
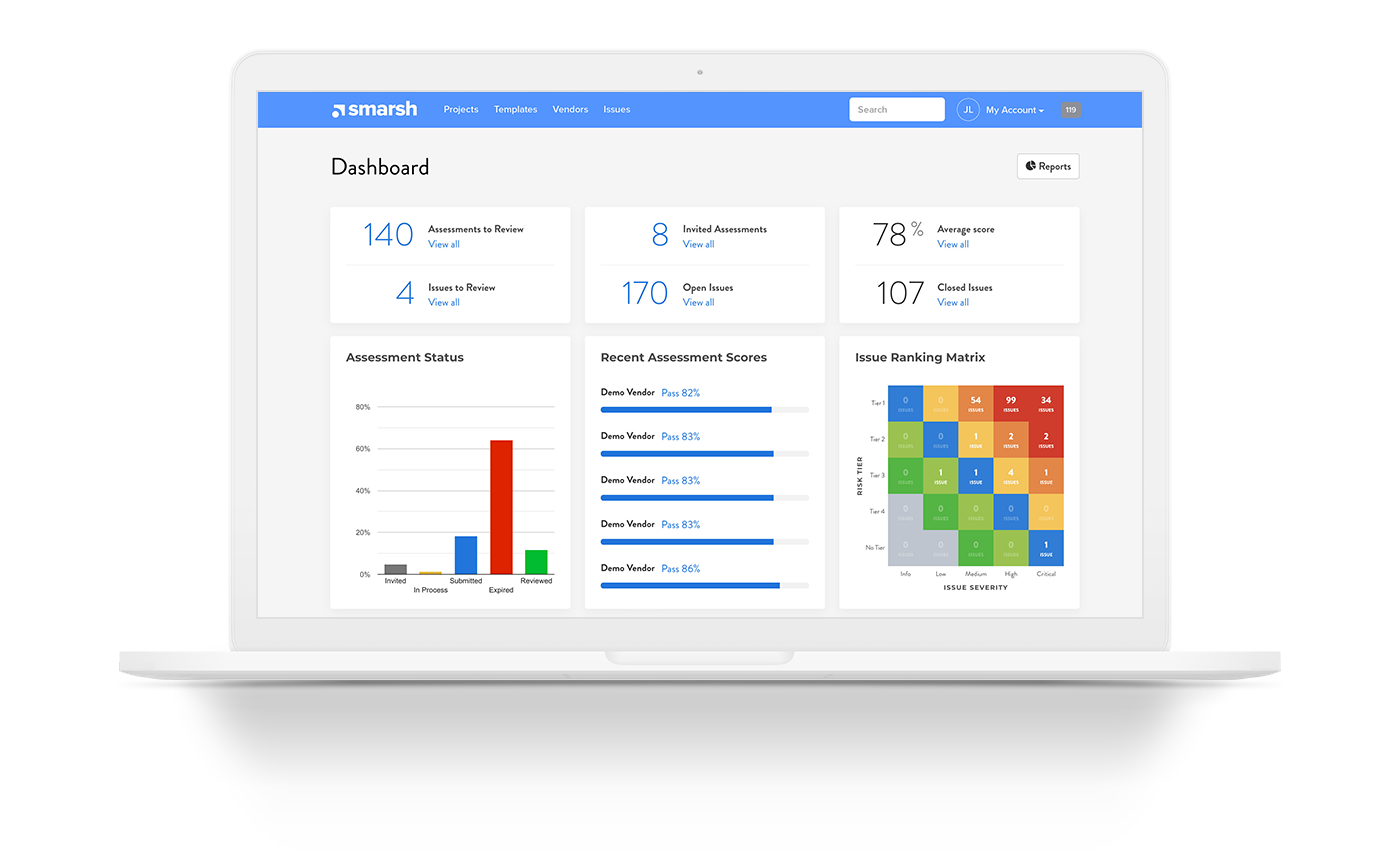
Review vendors, manage remediations, create reports and more from a single cloud-based platform. Easily manage vendors that have access to business-critical data from one centralized database.
Increase vendor risk assessment efficiency up to 70%
Automate time-consuming tasks based on vendor responses.
- All answers are automatically scored and filtered by risk rating
- All remediation tickets are automatically generated and stored in a library
- Get on-demand reporting for every level of your organization
Streamline risk remediation and management
Easily maintain auditable tracking of remediation plans and validation documentation.
Get real-time metrics on your vendor risk management program
Standardize your organization's approach to risk management by connecting teams with cross-functioning reports.
Manage and customize your 3rd party risk assessments
- Choose your own assessment questionnaire or use our licensed content.
- Assign assessments to third parties, manage access, and track status
- Quickly comment, remediate and score responses and compare them to industry benchmarks
Monitor risk at every stage
Easily track progress, manage communications, and get updates on remediation throughout the assessment process.
Vendor Risk Management Offerings
Smarsh offers three levels of solutions to fit your business needs.

Tech
- End-to-end access to the Smarsh VRM software platform, workflow and all features including complete vendor registry, assessment distribution, weighted categories, autoscoring of responses, vendor scoresheets, and reporting including vendor comparison reports

Tech Plus
- Access to the VRM software platform included in Tech
- Smarsh acts as the project manager throughout your engagement
- During the assessment period, Smarsh follows up with vendors and answers their questions and notifies you of all completed assessments that are ready for review
- Smarsh will summarize all progress made across your program in a regularly scheduled update communication

Managed
- Access to the VRM software platform and all its features included in Tech and Tech Plus
- Smarsh performs a security review of the assessment, provides comments, and identifies areas for follow-up within the platform
- Smarsh will score each question and provide a high-level summary of the results
- Smarsh will create follow-up tickets (“Issues” in the platform) based on the items approved by the customer.
Ready to automate your third-party risk strategy?
Complete your cybersecurity strategy by improving how you assess, evaluate and manage your vendor risk. Start a conversation with our third-party risk management experts today.